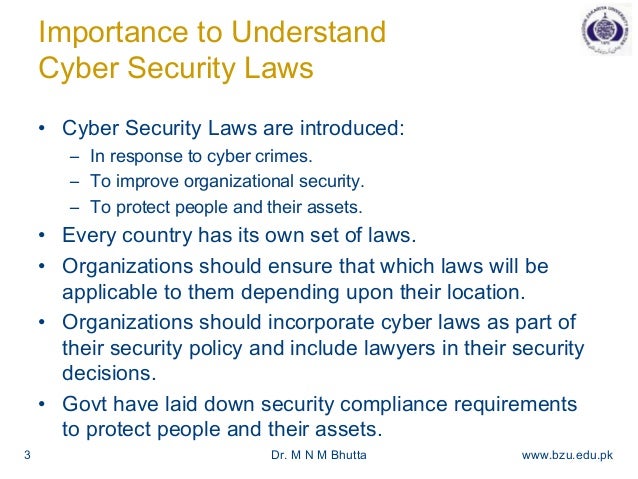
Cyber Security Laws - Cybersecurity Policy Characteristics Successful Cyber Security
Cybersecurity Policy Characteristics Successful Cyber Security
New Laws To Strengthen Uk Cybersecurity Provisions .
The Regulatory Landscape How Memcyco Helps Organizations Stay Compliant .

Cybersecurity Laws And Regulations Part 1 John Bandler .

Cyber Security Law Top 5 Cyber Security Laws Everyone Should Know .

Are You Up To Date With The Latest Cybersecurity Laws .

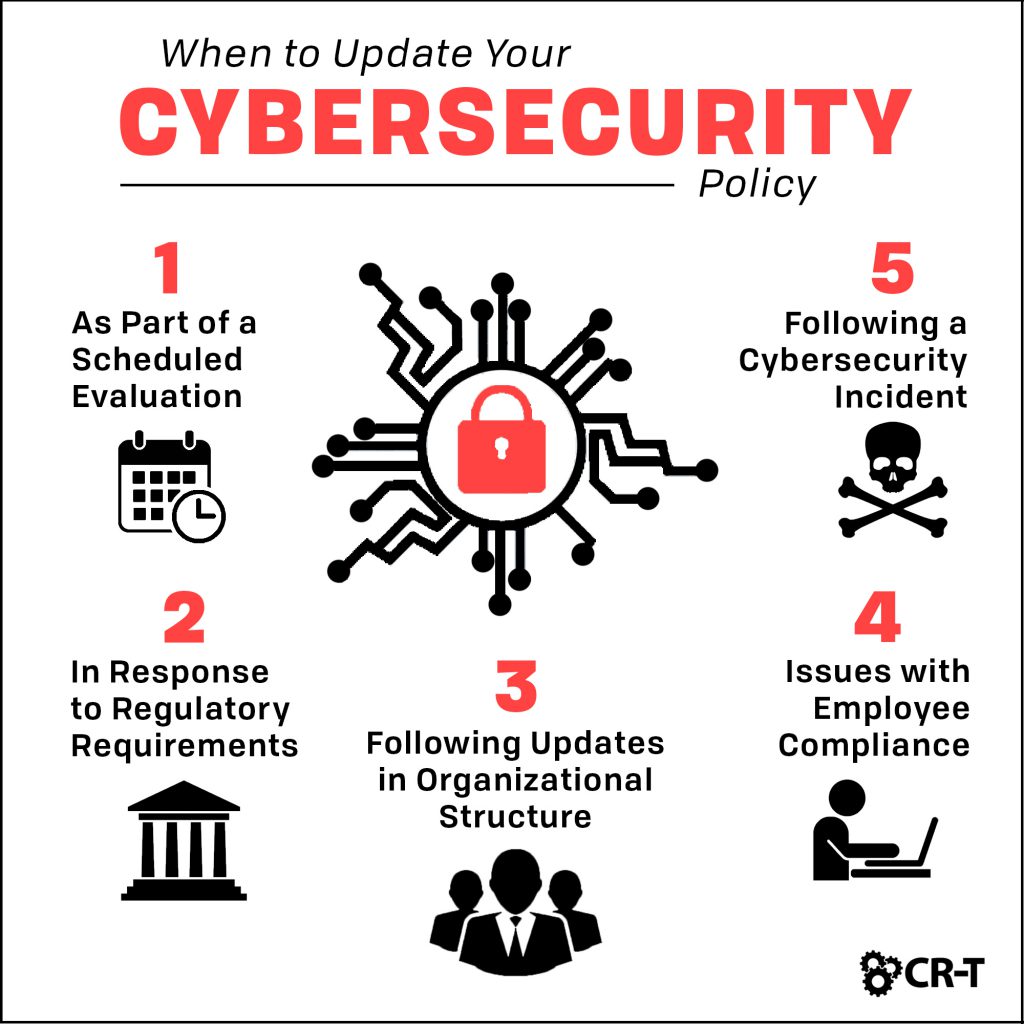
What Is Cyber Policy Infographic .

Cyber Security Laws A Complete Guide .
United States Cyber Security Laws Critical Path Security .
Book With Cyber Security Laws Justice And Legislation Concept Stock .
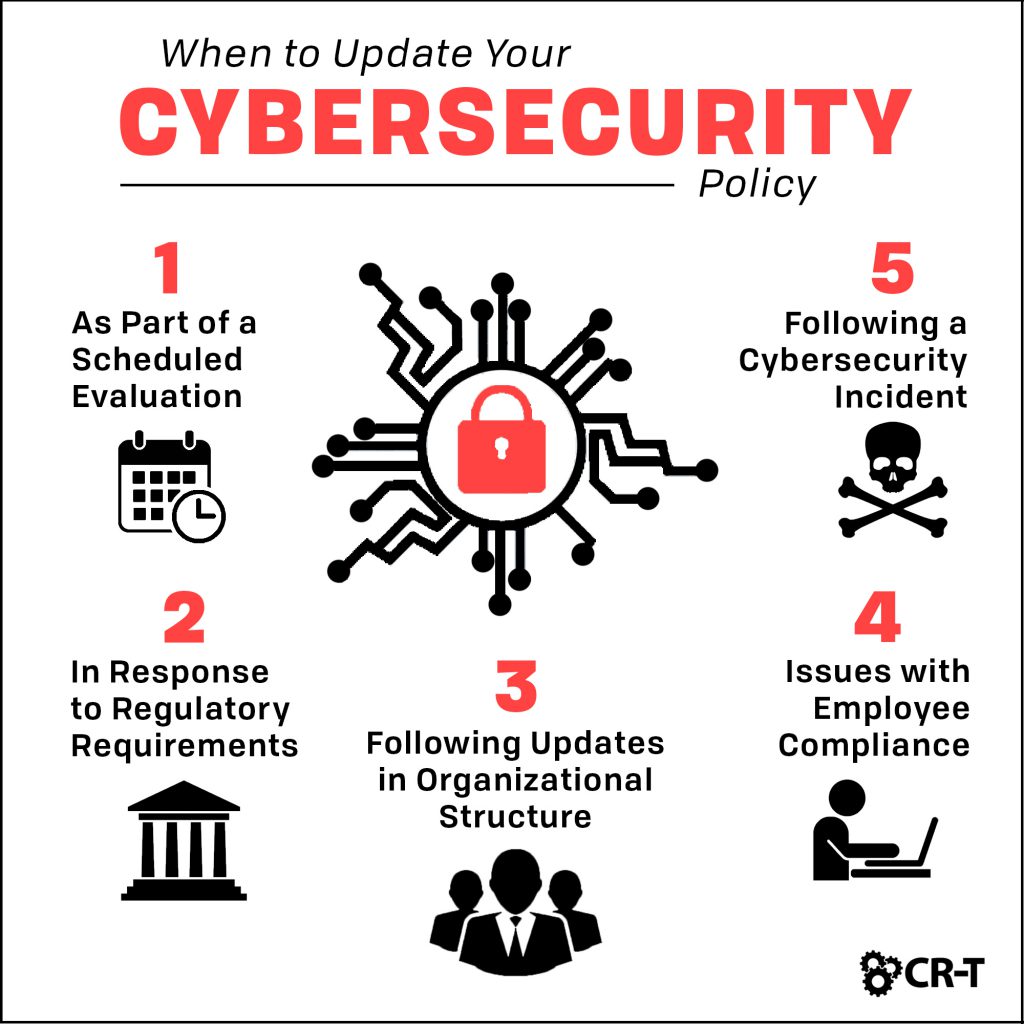
Cybersecurity Policy Characteristics Successful Cyber Security .
The Ever Evolving Cyber Laws .

Cyber Laws And Modern Changes Thecyberdelta .

Cybersecurity Laws A Complete Overview Cyberexperts Com .

Cyber Law Course Specializations Career Options And Job Prospects .

Cyber Security And The Indian Cyber Laws With Its Details .

Key Cyber Security Laws In India Agiledock .
Cyber Security Law Digital Legislation 2d Illustration Stock .

Important Cyber Security Laws You Should Know By State .

Top 10 Cyber Security Laws Techyv Com .

Cyber Security And Laws Csl 7th Semester January 2021 Mumbai University .
.png?width=1104&name=Inline%20-%20Cyber%20Security%20LinkedIn%20(002).png)
What Do The Uk S Cybersecurity Plans Mean For Companies .

On Cybersecurity Laws And Their Interpretations .

Major Cybersecurity Laws That Us Businesses Must Know Halt Org .

Romania 39 S New Cybersecurity Law Continues To Generate Controversies .
Cyber Security Laws And Regulations .
Cyber Security Laws .

Cyber Security Laws And Regulations .

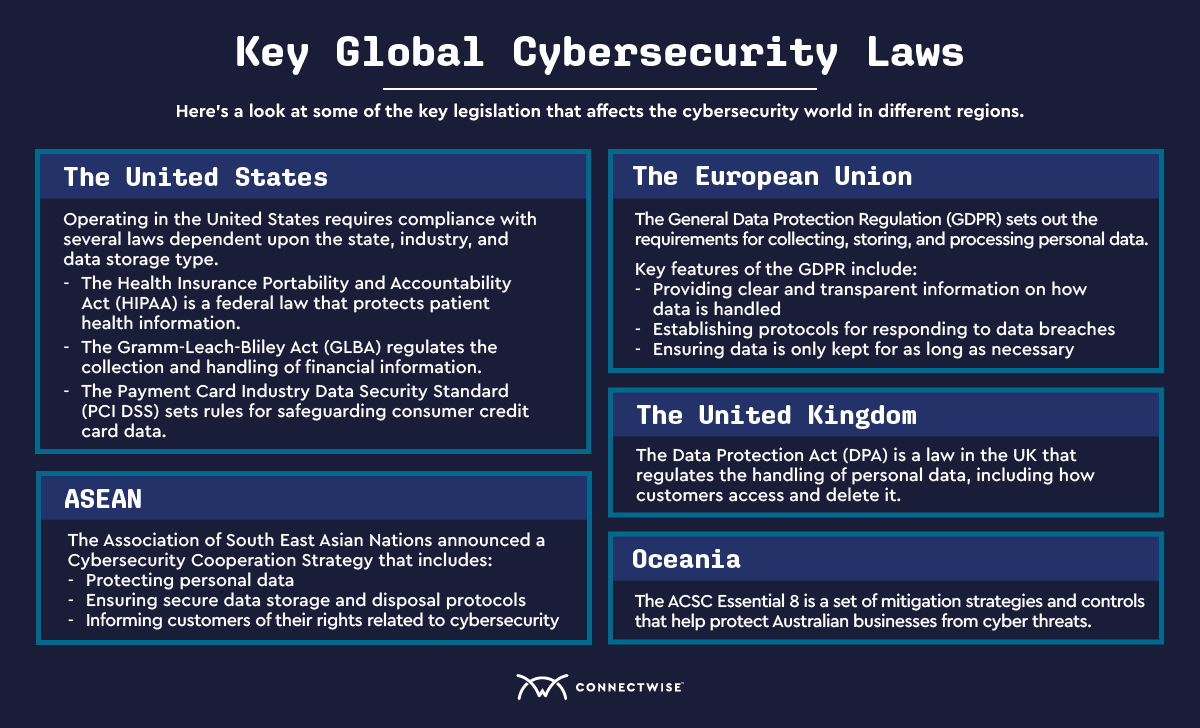
Cyber Security Laws Around The World Securinc .

Cybercrime Module 8 Key Issues International Cooperation On .

Cyber Security And The Indian Cyber Laws With Its Details .

List Of Cybersecurity Regulations In The European Union Upguard .

80 Africa Cybersecurity Statistics And Trends 2024 .
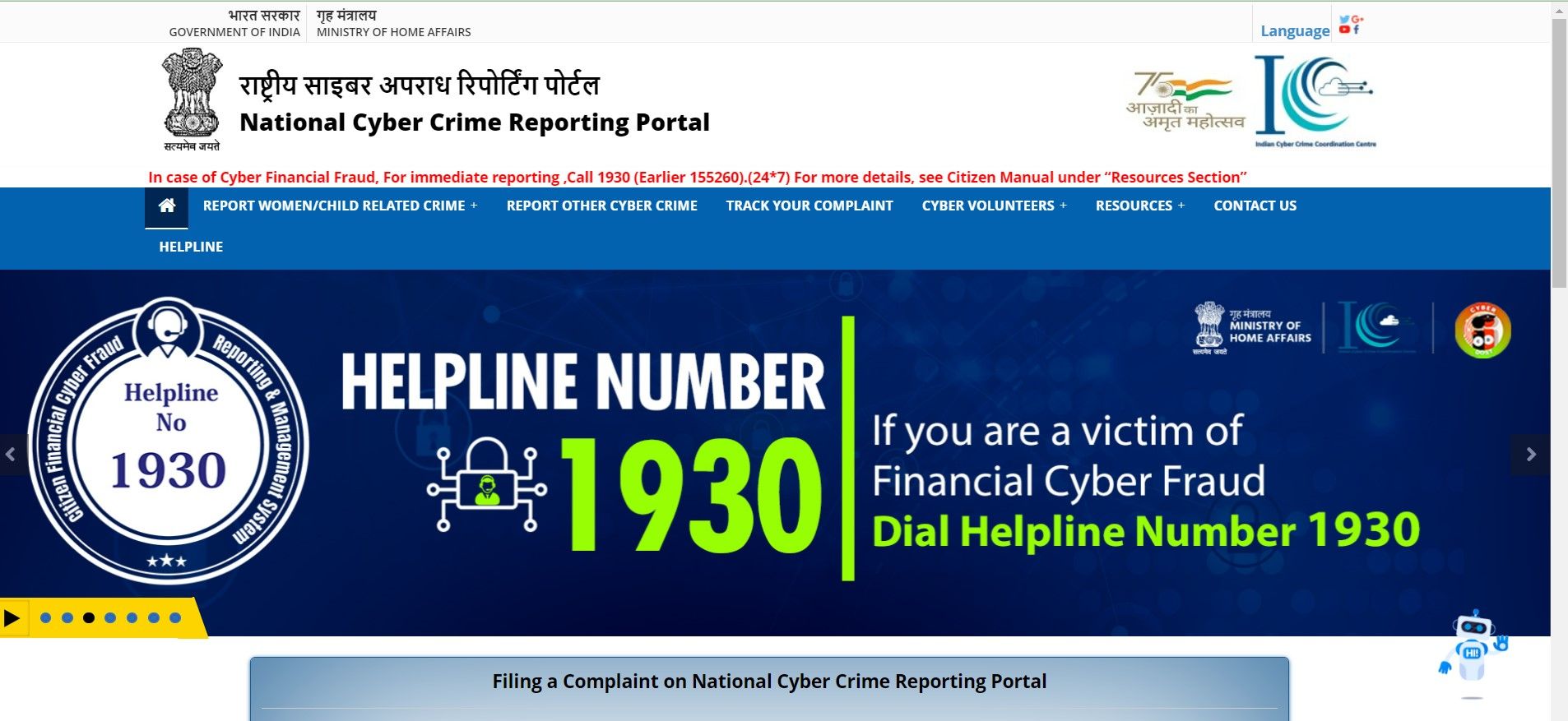
Cyber Security Laws In India Part 2 .

New Cybersecurity Regulations 2 Follow Dr Erdal Ozkaya .

News Cil Organises Workshop On Cyber Security Cyber Laws Psu Connect .
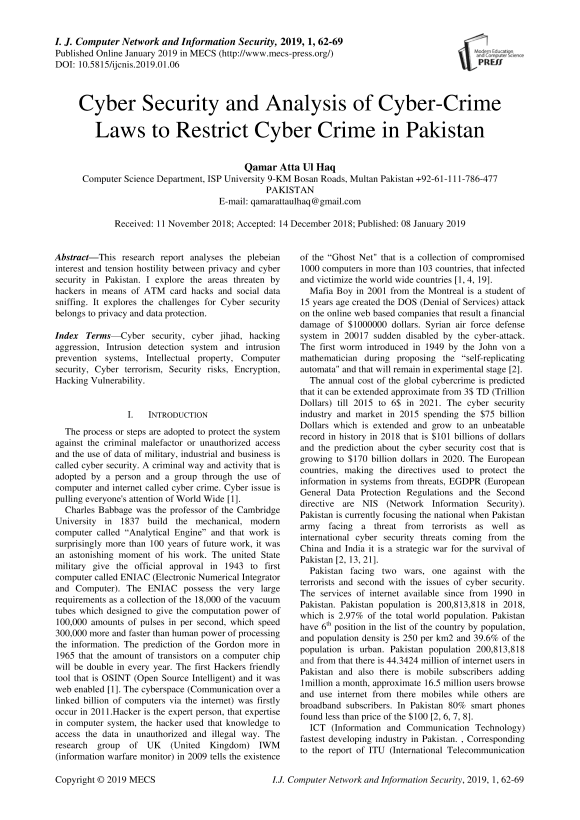
Cyber Security And Analysis Of Cyber Crime Laws To Restrict Cyber Crime .

8 Essential Policies Procedures For Improved Cyber Security Kbi .

To Keep Up With Cybersecurity Laws Go 39 Federal First 39 Threatshub .
Cyber Security Laws .

Guide To Cyber Law Degrees Finding The Best Cybersecurity Law Degree .
Cyber Crime Cyber Law Cyber Ethics Commandments Piracy Imposter .
Cybersecurity Laws Understanding Measures Against Cybercrime .
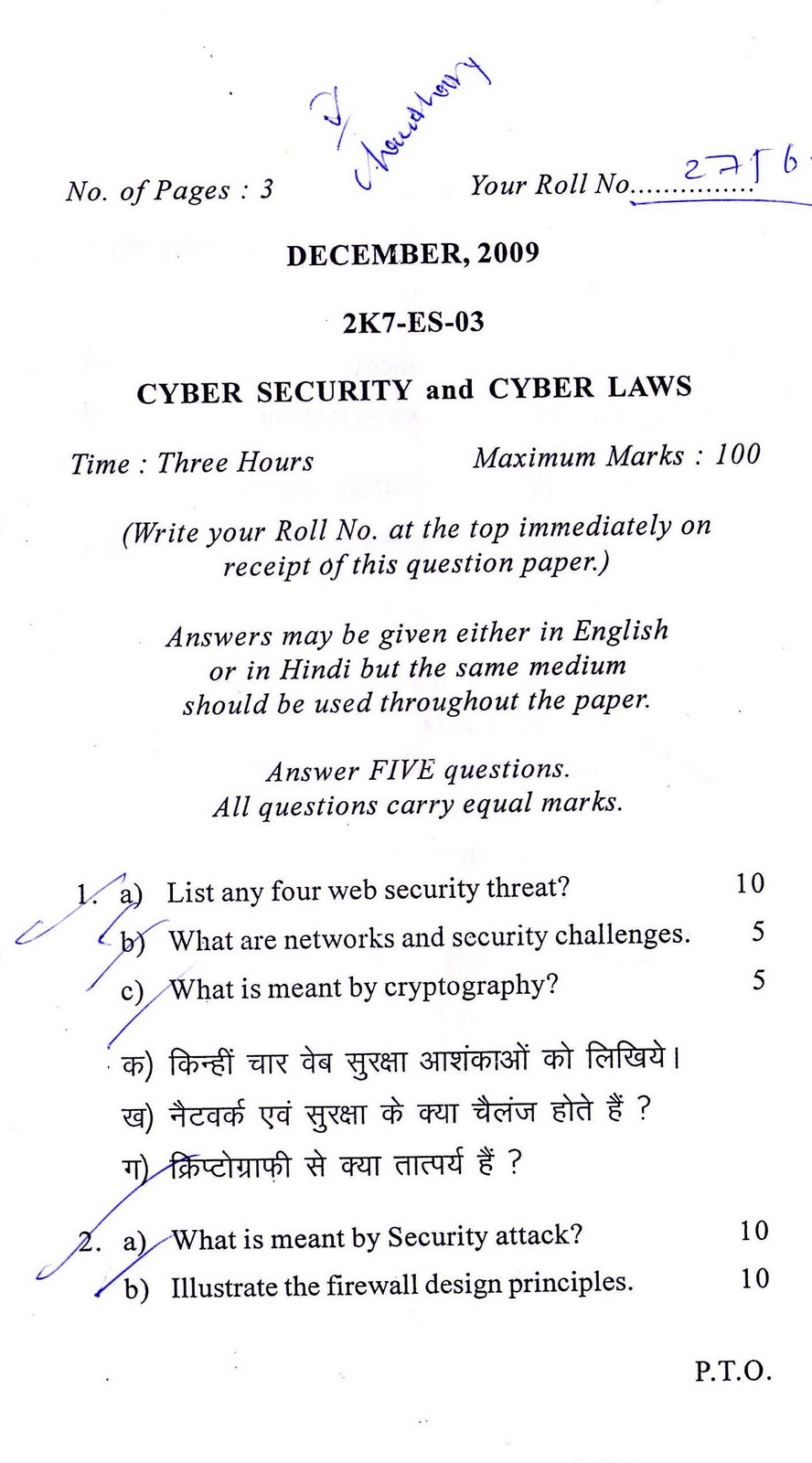
Download Sample Paper Of Cyber Security Cyber Laws Delhi .

Pdf Protecting Our Critical Infrastructure Understanding New Cyber .

Online Ipr Infringements And Information Technology Act 2000 J P .
.webp)
Cyber Laws In India Cybersecurity Crime Laws Regulations .

Cyber Security Policies Dataflair .

Data Security Laws Questioned After Optus Cyber Attack .
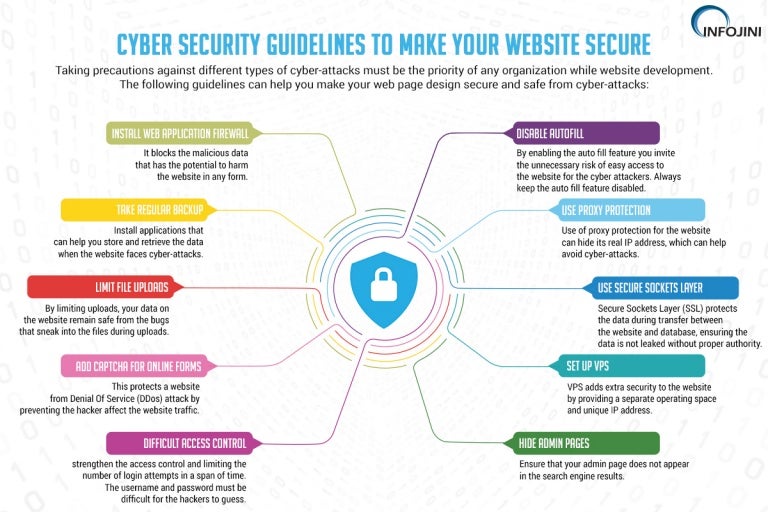
Cyber Security Guidelines For Your Website Infographic .

Laws Regulations For Cybersecurity Impacting Uk Businesses .
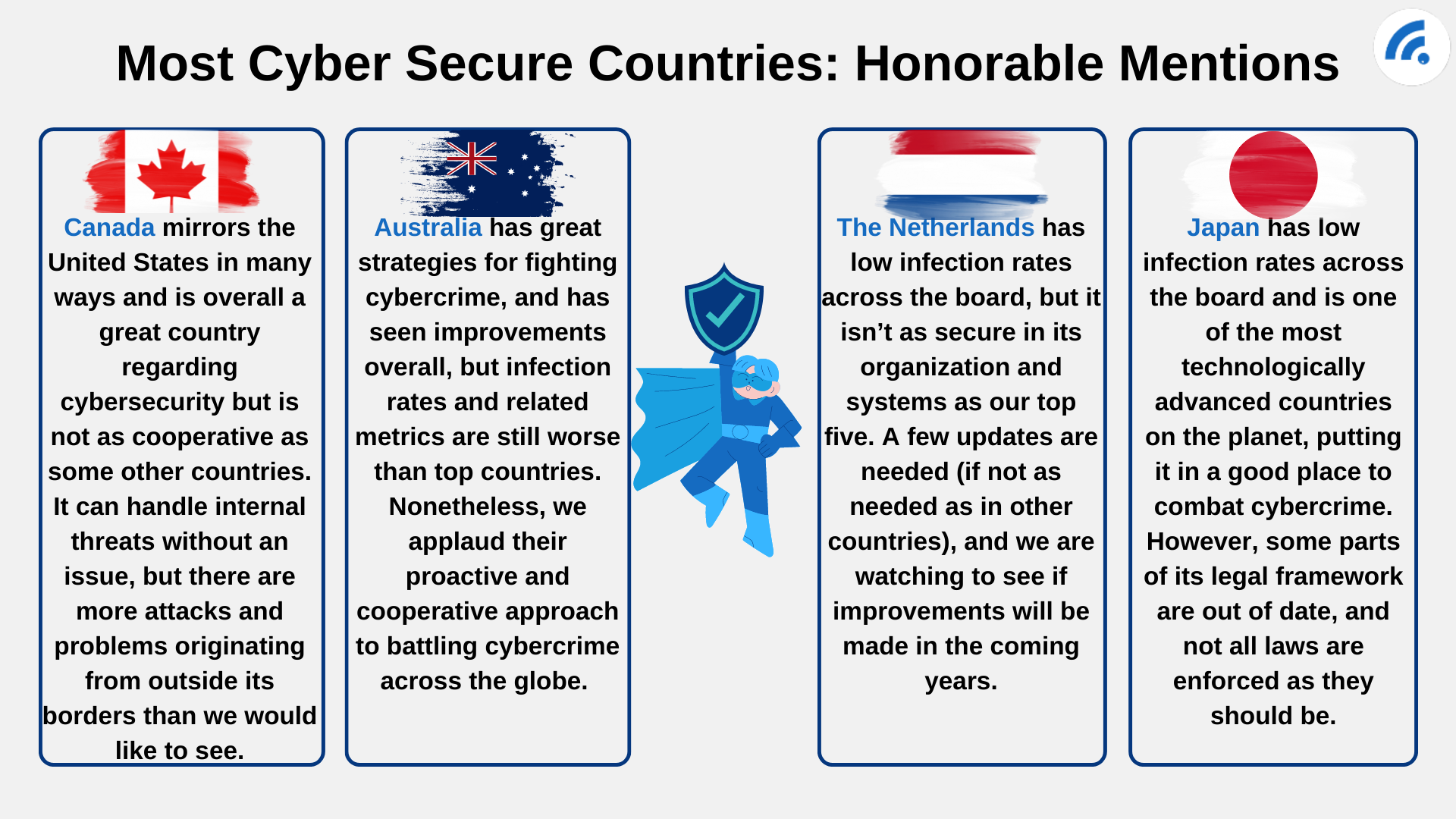
Know The Risk The Best And Worst Countries For Cybersecurity .
Cyber Security Mehak Alamgir .

Global Cybercrime And Cybersecurity Laws And Regulations Issues And .
Buy Cyber Security And Cyber Laws Book Alfred Basta 9387511677 .

Round Table On Cyberlaw Cybercrime Cybersecurity .
Pdf Cybersecurity Law And Regulation .

All You Need To Know About Indian Worldwide Cyber Laws .

A Glance At The United States Cyber Security Laws .
Information Security And Cyber Laws Buy Information Security And Cyber .

Brief Guide To Understand The Importance Of Cyber Laws In India .
- tide chart shelter cove ca
- new york state child support standards chart 2017
- world chart show top 20 list
- battery voltage chart 12v
- dansko 37 size chart
- r12 pressure temperature chart
- nifty future live chart google finance
- reading levels correlation chart grades k 6
- token system chart
- free approach charts
- lacrosse shoulder pad sizing chart
- weight max 5 58 17 feeding chart
- chesapeake energy arena seating chart pbr
- valspar tintable chalkboard paint color chart
- lions 2017 depth chart
- wedding table seating chart template free
- mac studio fix powder plus foundation color chart
- civil engineering charts
- pedigree chart practice
- green chart
- born baby injection chart
- j mode usa size chart
- rc servo comparison chart
- infant motor skills development chart
- surface chart excel definition
- carrot chart
- yuan vs usd chart
- wachovia virtual seating chart
- pnc park seating chart luxury suites
- brass specifications chart